Android banking Trojan tricks victims into submitting selfie holding their ID card
While some payment card companies like Mastercard have switched to selfies as an alternative to passwords when verifying IDs for online payments, häçkers have already started taking advantage of this new security verification methods.
 Researchers have discovered a new Android banking Trojan that masquerades primarily as a video plugin, like Adobe Flash Player, ****ographic app, or video codec, and asks victims to send a selfie holding their ID card, according to a You do not have permission to view the full content of this post.
Log in or register now. published by McAfee.
Researchers have discovered a new Android banking Trojan that masquerades primarily as a video plugin, like Adobe Flash Player, ****ographic app, or video codec, and asks victims to send a selfie holding their ID card, according to a You do not have permission to view the full content of this post.
Log in or register now. published by McAfee.
The Trojan is the most recent version of You do not have permission to view the full content of this post. Log in or register now. that has been labeled as one of the most dangerous Android banking Trojans known today, according to Kaspersky Lab Anti-malware Research Team. Once successfully installed, the trojan asks users for a number of device's permissions to execute the malicious code and then waits for victims to open apps, specifically those where it would make sense to request payment card information.
Acecard s†éáls your Payment Card and Real ID details
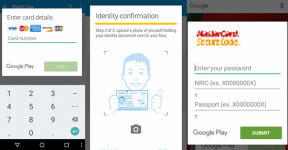
The banking trojan then overlays itself on top of the legitimate app where it proceeds to ask users for their payment card number and card details such as card holder's name, expiration date, and CVV number.
"It displays its own window over the legitimate app, asking for your credit card details," explains McAfee researcher Bruce Snell. "After validating the card number, it goes on to ask for additional information such as the 4-digit number on the back."
Once this is done, the trojan then looks to obtain users' personal information, including their name, date of birth, mailing address, for "verification purposes," and even requests a photo of the front and back sides of their ID card. After this, the Trojan also prompts to ask users to hold their ID card in their hand, underneath their face, and take a selfie.
häçkers can make îllégâl Transfers and Take Over your Online Accounts
All these pieces of information are more than enough for an attacker to verify îllégâl banking transactions and s†éál access to victims' social media accounts by confirming the stolen identities. So far this version of Acecard Android banking Trojan has impacted users in Singapore and Hong Kong.
This social engineering trick of Trojan obviously is not new, and any tech-savvy users would quickly catch this malicious behavior as there is no reason for Google to ask for your ID card. But the trick still works with non and less technical users. Since all of these fake apps have been distributed outside of Google Play Store, users are strongly advised to avoid downloading and installing apps from untrusted sources. Besides this, users should pay attention to the permissions apps are asking for.
Most importantly: No app needs a photo of you holding your ID card except perhaps a mobile banking service. So, always be cautious before doing that.
While some payment card companies like Mastercard have switched to selfies as an alternative to passwords when verifying IDs for online payments, häçkers have already started taking advantage of this new security verification methods.
 Researchers have discovered a new Android banking Trojan that masquerades primarily as a video plugin, like Adobe Flash Player, ****ographic app, or video codec, and asks victims to send a selfie holding their ID card, according to a You do not have permission to view the full content of this post.
Log in or register now. published by McAfee.
Researchers have discovered a new Android banking Trojan that masquerades primarily as a video plugin, like Adobe Flash Player, ****ographic app, or video codec, and asks victims to send a selfie holding their ID card, according to a You do not have permission to view the full content of this post.
Log in or register now. published by McAfee.The Trojan is the most recent version of You do not have permission to view the full content of this post. Log in or register now. that has been labeled as one of the most dangerous Android banking Trojans known today, according to Kaspersky Lab Anti-malware Research Team. Once successfully installed, the trojan asks users for a number of device's permissions to execute the malicious code and then waits for victims to open apps, specifically those where it would make sense to request payment card information.
Acecard s†éáls your Payment Card and Real ID details
The banking trojan then overlays itself on top of the legitimate app where it proceeds to ask users for their payment card number and card details such as card holder's name, expiration date, and CVV number.
"It displays its own window over the legitimate app, asking for your credit card details," explains McAfee researcher Bruce Snell. "After validating the card number, it goes on to ask for additional information such as the 4-digit number on the back."
Once this is done, the trojan then looks to obtain users' personal information, including their name, date of birth, mailing address, for "verification purposes," and even requests a photo of the front and back sides of their ID card. After this, the Trojan also prompts to ask users to hold their ID card in their hand, underneath their face, and take a selfie.
häçkers can make îllégâl Transfers and Take Over your Online Accounts
All these pieces of information are more than enough for an attacker to verify îllégâl banking transactions and s†éál access to victims' social media accounts by confirming the stolen identities. So far this version of Acecard Android banking Trojan has impacted users in Singapore and Hong Kong.
This social engineering trick of Trojan obviously is not new, and any tech-savvy users would quickly catch this malicious behavior as there is no reason for Google to ask for your ID card. But the trick still works with non and less technical users. Since all of these fake apps have been distributed outside of Google Play Store, users are strongly advised to avoid downloading and installing apps from untrusted sources. Besides this, users should pay attention to the permissions apps are asking for.
Most importantly: No app needs a photo of you holding your ID card except perhaps a mobile banking service. So, always be cautious before doing that.
Attachments
-
You do not have permission to view the full content of this post. Log in or register now.